A key part of business and personal security is being careful of emails that are designed to steal your data, bank accounts, or even your identity! Phishing is an attempt to manipulate you (the recipient) into handing over your data, or to give out access to data under fraudulent circumstances. These sorts of manipulations come in many forms, such as vishing (voice phishing), SMS phishing, or fax phishing. These scams are called phishing because the attacker is effectively sending you bait in the hope you will take it.
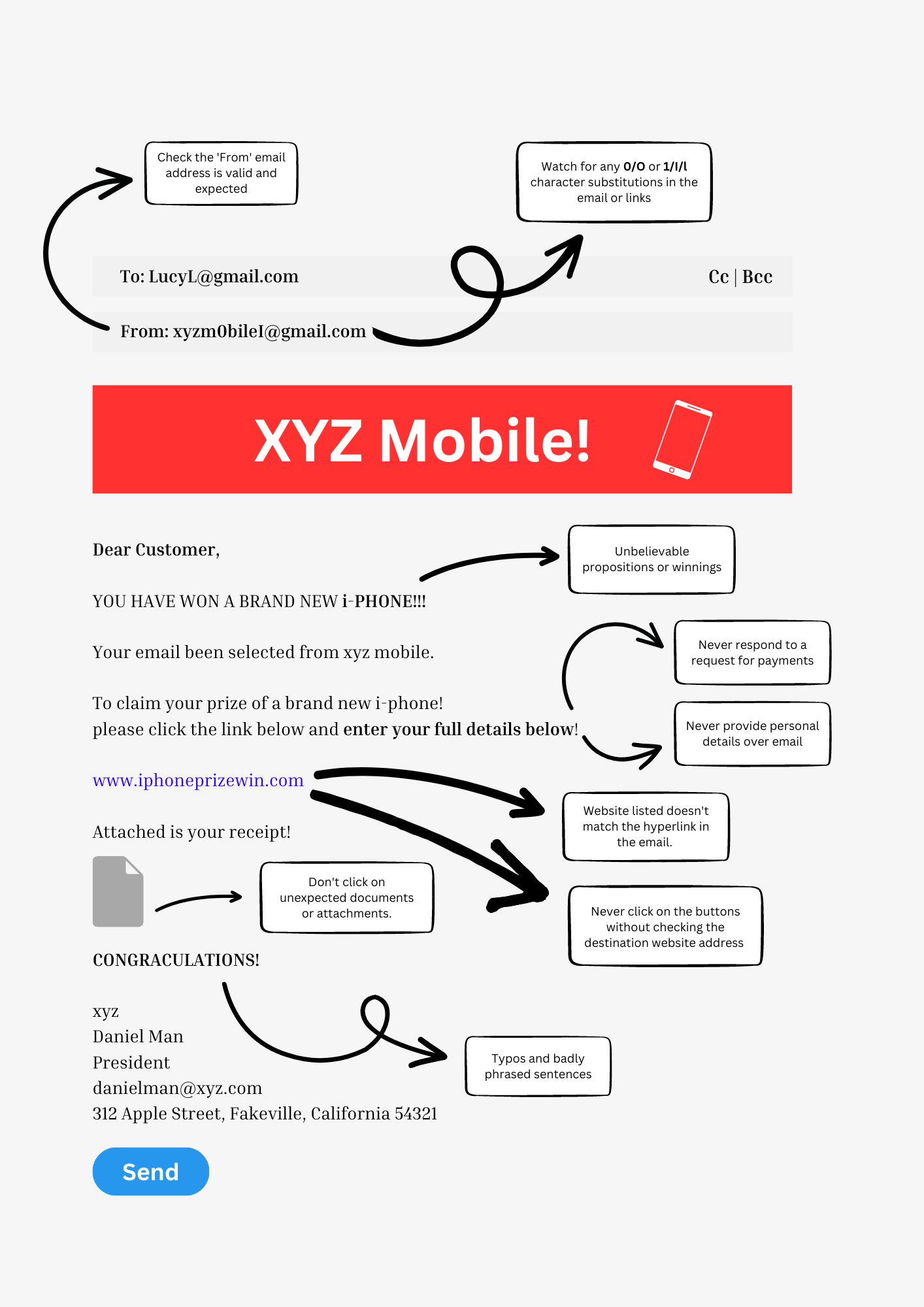
An email phishing scam will use trusted authoritative business branding, such as banks or government departments, to try and make their emails look as polished and professional as possible. Some scams use psychological tricks to filter the recipients, so they can find unsuspecting targets.

Tips to Spot & Stay Protected from Phishing Scams
Read Your Email Carefully – Do Not Skim Read!
You can spot phishing emails in many ways, but the first rule to spotting a phish is to read your email carefully.
- Do you recognise the email address?
- Is the Reply-to address is legitimate (noreply@mygov.au vs noreply@my0v.au)
- Are the links are legitimate (www.westpac.com.au vs www.wes1pac.com.au)
- Have you communicated with this company by email before?
- Are you expecting the email?
- Is this from a person or is it a blanket email to a large number of people?
Be very careful of any blanket emails, and if you have any doubts, mark them as spam and notify your ICT contact, or contact the business to check whether the email is genuine.
Never use the links or contact details provided in an email until you are 100% sure that the email is valid.
Never click on an attachment!
An attachment can be the virus software, ready to install. It can also be a keylogging program, which can record everything you type and then send that data secretly to a home base, where people can then look for passwords and login codes. It can be ransomware, which is when your computer is locked, and you can’t access it again unless you enter your credit card details.
Only open attachments if you are expecting them, from a trusted source, and they have been scanned by your virus scanner before opening.
Typos and Spelling Errors in Emails
There’s a psychological reason for those typos and spelling errors – it’s a way of filtering out the recipients of the email. The reasoning is that if you’re educated enough to spot the errors, then you’re unlikely to fall for the scam, and so you discount it and move on. Any spelling errors, grammar mistakes and random characters are warning signs.
How to Check Links in Email
If the email is requesting you click on a link, or provides a link for verification, you can check where the link will take you by waving your mouse over the hyperlink. In most email programs, the actual link will show up down in the right hand corner of the screen. If you’re using a web browser to access your email, this may show in the bottom left corner, or float next to the link when you wave the mouse over it.
Use this link here to locate where the preview link information appears: You should see this text is highlighted and the URL is to empower ICT.

What to do when You Receive a Phishing Email
Notify your ICT department. At Empowered ICT, we can check the source of the email, and block it. We can also remove it from some email files, so letting us know as soon as possible is always the best step. We can also notify relevant authorities, and add the email to our blacklist to ensure no one else is troubled by it.
What to do if you fell Victim to a Phishing Email
Notify your ICT department immediately, and give accurate details on what has happened, what your actions were, and what access or data has been inadvertently shared. If you have provided your credit card details, you will need to contact your bank immediately. Discuss with your ICT team whether to file a report with the ACCC Scamwatch, and record details in your diary or calendar for future reference.
https://www.scamwatch.gov.au/report-a-scam
If you have fallen victim or are worried your company will be vulnerable, speak to one of our consultants today. We can help prevent, reduce and block phishing attacks as well as provide educational material. Awareness is key, and everyone in a business is responsible for data security.
Catch us on popular social media channels. Get in touch now Empower ICT – Sales & Enquiries | 1300 850 210

ADDRESS
Perth: 4/353 Cambridge St, Wembley WA 6014
Melbourne: Suite 4, 1-3 Compark Circuit, Mulgrave, VIC 3170
Mandurah: 2/24 Rouse Road Mandurah, WA 6210
SALES & ENQUIRIES
8:00 AM – 5:00 PM MON-FRI
TECHNICAL SUPPORT
24/7